Respawn
 Almost unnoticeable among the noise and fury of this week in British politics (which required a thorough review of Yes, Minister to parse), several initiatives reopened old wounds.
Almost unnoticeable among the noise and fury of this week in British politics (which required a thorough review of Yes, Minister to parse), several initiatives reopened old wounds.
First off, Ars Technica reports that Privacy Shield, the replacement for the late, not-so-much-lamented Safe Harbour, looks set for approval. Both European and American businesses have been operating in limbo while awaiting a new legal framework. The court's key complaints about Safe Harbor were that data transferred to the US could not be protected from NSA bulk surveillance and that EU citizens lacked access to redress within the US. To remedy the situation, the US passed the Judicial Redress Act, which some observers argue doesn't help much because of the practical difficulties of exercising the limited rights it grants. These two points were part of the basis of the Article 29 Working Party's criticism of the draft Privacy Shield. Now it seems set to pass, we'll have to wait and see what the courts think.
 Meanwhile, the model contracts that companies have been using to fill the gap have also been found inadequate in a draft decision by the Irish data protection authority. If this view is upheld by the courts, it could leave both European and American businesses in trouble. As a whole, the situation has led Dutch data protection expert Lokke Moerel to ask whether the EU is veering into protectionism. European companies, as much as US ones, need to perform data transfers. In the piece linked above, Moerel suggests that the EU is exercising a double standard - especially since the US and EU are apparently able to agree on data protection safeguards for the purposes of law enforcement, just not for commercial purposes.
Meanwhile, the model contracts that companies have been using to fill the gap have also been found inadequate in a draft decision by the Irish data protection authority. If this view is upheld by the courts, it could leave both European and American businesses in trouble. As a whole, the situation has led Dutch data protection expert Lokke Moerel to ask whether the EU is veering into protectionism. European companies, as much as US ones, need to perform data transfers. In the piece linked above, Moerel suggests that the EU is exercising a double standard - especially since the US and EU are apparently able to agree on data protection safeguards for the purposes of law enforcement, just not for commercial purposes.
 Meanwhile, we had almost entirely forgotten about the Digital Economy bill, which was announced in May in the Queen's speech. The key controversial elements look set to be the provisions regarding copyright - the bill seeks to raise the maximum prison term for online copyright infringement from two years to ten - and access to pornography. The proposal is to require websites to implement controls barring minors from access; industry discussions about how to do this have been underway for some time. A new Age Verification Regulator will be able to fine sites up to £250,000 or 5 percent of turnover.
Meanwhile, we had almost entirely forgotten about the Digital Economy bill, which was announced in May in the Queen's speech. The key controversial elements look set to be the provisions regarding copyright - the bill seeks to raise the maximum prison term for online copyright infringement from two years to ten - and access to pornography. The proposal is to require websites to implement controls barring minors from access; industry discussions about how to do this have been underway for some time. A new Age Verification Regulator will be able to fine sites up to £250,000 or 5 percent of turnover.
Next, in the process of announcing a new consultation on sharing medical data, the government also said it was closing down the care.data program that caused so much trouble back last year. The consultation asks for opinions about a bunch of proposed security standards and from the sounds of it the intention is to give patients more flexible options for consent. Nonetheless, perhaps in part because of the amount of political posturing that's gone on in the wake of the EU referendum vote, it seems logical to fear that "closing care.data" may wind up meaning "renaming and relaunching care.data". I hope not. I hope we wind up with a really good solution to sharing medical data so everyone's health benefits while genuinely protecting patient privacy and trust. In May, the Ponemon Institute's sixth annual study on the privacy and security of healthcare data found that nearly 90 percent of the organizations surveyed had at least one breach in the last two years - and 45 percent had more than five. The leading cause of breaches is criminal activity such as ransomware, DDoS attacks, and malicious insiders are a key problem.
Doubtless plenty of advisers will pop up to tell the government and NHS how to do security properly. The bigger worry is that, like the paper BoingBoing highlighted recently, the efforts to protect security will be devised in such a user-unfriendly way that healthcare workers on the ground will be forced to ignore them to avoid putting patients at risk. These are the kinds of issues that Angela Sasse and others have worked on for years: security has to work with and for people. Nowhere is it clearer than in healthcare that security has to be designed with the understanding that it has to support, rather than hinder, the non-security functions that are most people's primary jobs.
Finally, some months back, I said much the same about Hillary Clinton's email server, and got some pushback (on Facebook) by those who felt her complaint was specious. This week, the eminent computer science professor and security authority Eugene Spafford commented on the absence of discussion of whether the rules applied to Clinton were appropriate. That absence is still notable: instead, people are wrangling over James Comey's report and his discinclination to bring criminal charges against Clinton, the news that the hacker who claimed to have hacked her server actually didn't, and exactly how many of the emails she sent through her server were classified at the time when she sent them (three, Comey told Congress). And so, the BBC reports, the State Department will now reopen its investigation into the matter. The one good side of this is that for the rest of this year - and probably into next - email security is going to receive an unprecedented amount of national attention, even among politicians who don't use it. Maybe security will genuinely improve as a result.
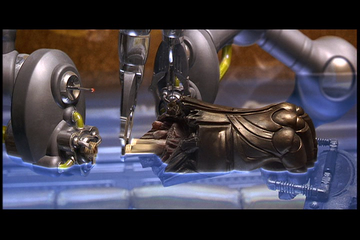
Illustrations: Rebuilding from a DNA strand in The Fifth Element; Lokke Moerel; the UK's 18-rating logo.
Wendy M. Grossman is the 2013 winner of the Enigma Award. Her Web site has an extensive archive of her books, articles, and music, and an archive of earlier columns in this series. Stories about the border wars between cyberspace and real life are posted occasionally during the week at the net.wars Pinboard - or follow on Twitter.